SQL Server Default Port
SQL Server Default Port
The default port for the SQL Server Engine is 1433, which is a useful thing to know if you’re working as a Database Administrator (DBA) or Database Reliability Engineering (DBRE) type role.
Though-out my career I’ve seen SQL Server run on the default 1433 port 99% of the time. For the other 1 percent, it didn’t matter much to me what port it was using.
Occasionally as a DBA, you will need to arrange network line of sight (firewall rule changes) to be carried out by Network teams for MSSQL host-to-host connectivity. This is done via some request form a lot of the time, and we need to send source/destination addresses. Including IP addresses, we would also need to verify which port the SQL Server is using. Always best to double-check which MSSQL is running before submitting these types of requests, the demo below will help get this info.
We also need to consider the local Windows Firewall on each SQL Server host. The rule should be scoped to the individual IP connecting, or subnet (10.20.30.0\24, all 256 addresses).
SQL Server uses a lot of ports for various features & services, e.g. SQL Browser 1434 / SSIS 135. For anything beyond this basic SQL port info, MS Docs will provide you with what’s needed – there’s a lot, which I’m currently digesting at the time of writing.
Anyway, with network stuff out of the way, this post contains the following demos:
# How to Check Default SQL Server Port
# How to Add New Windows Firewall Rule for Default MSSQL Port (1433)
How to Check Default SQL Server Port
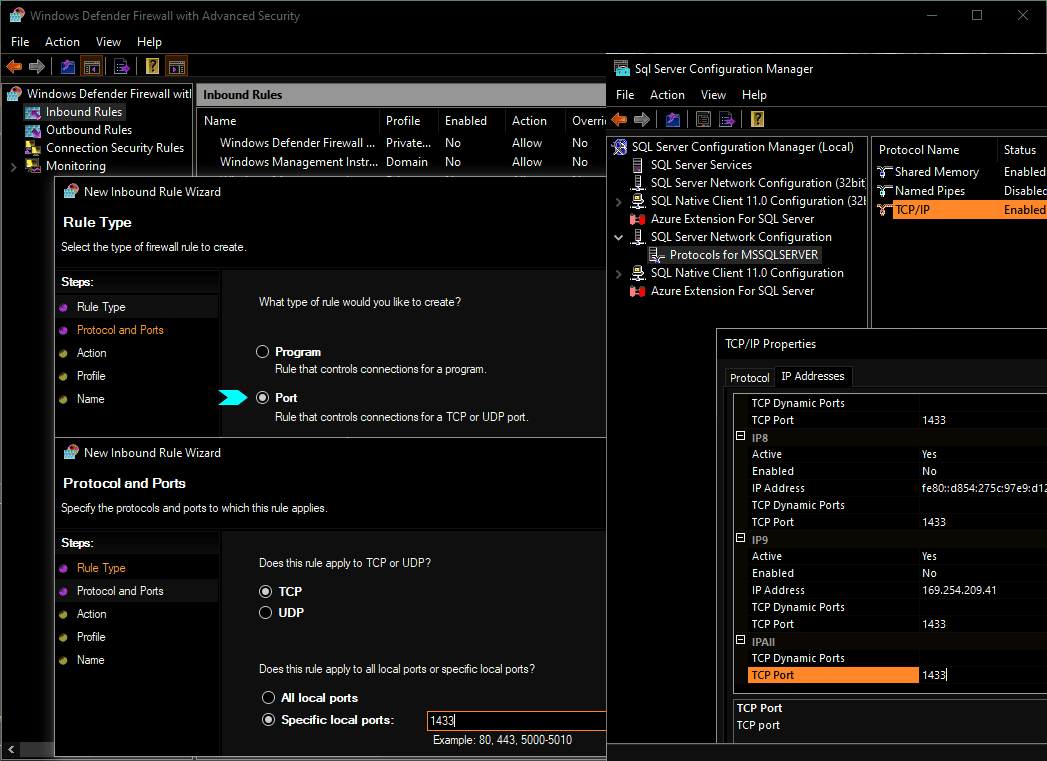
Open SQL Server Configuration Manager, which is accessible via the Start Menu on any SQL Server host.
Navigate as shown on the screenshot below, to SQL Server Network Configuration > Protocols for MSSQLSERVER > TCP/IP Properties > IP Address Tab –
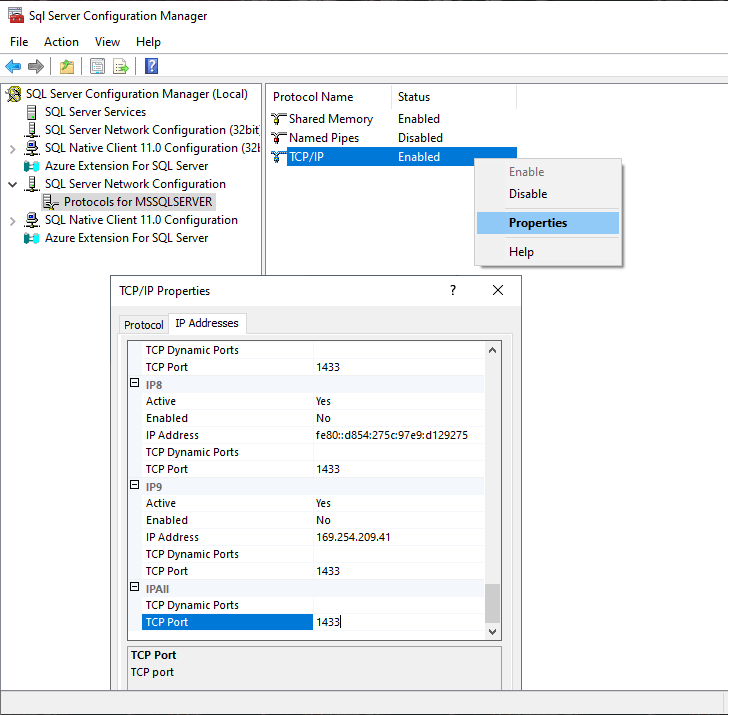
You can amend ports here too, but read MS Docs and test first if doing on Production, of course.
How to Add New Windows Firewall Rule for Default MSSQL Port
This is an added note on how to add the SQL Server 1433 Port & SQL Server Browser 1434 Ports. We can use the GUI >
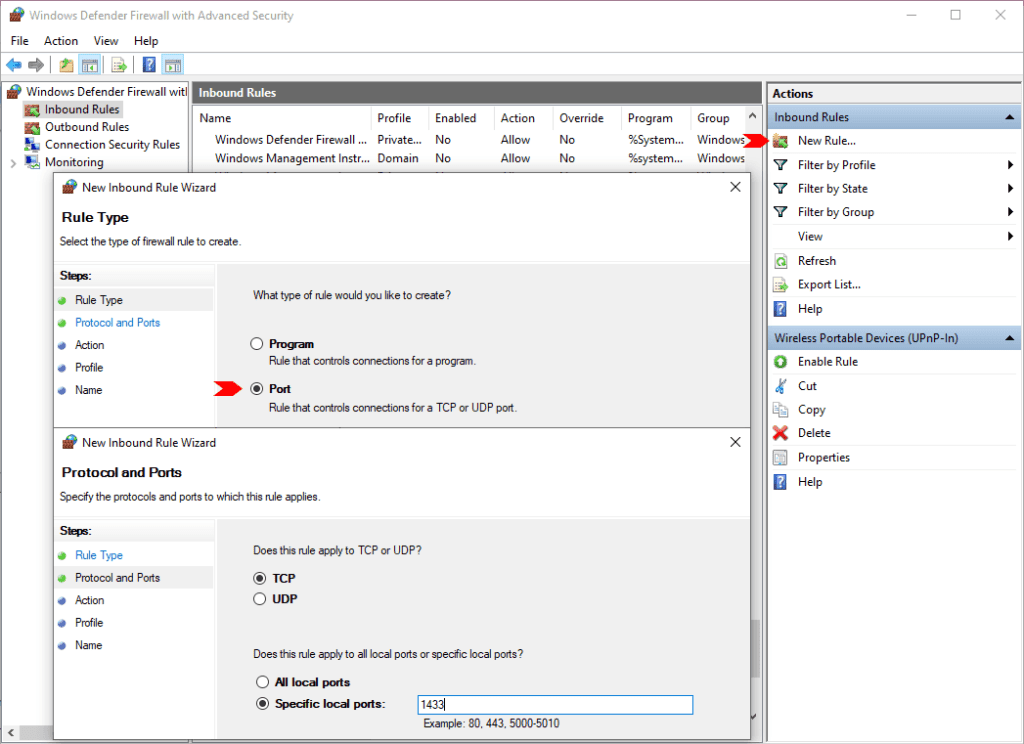
And we can do the same with PowerShell, using the New-NetFirewallRule cmdlet.
# Add SQL Server Local Firewall Rule New-NetFirewallRule -DisplayName "SQLServer default instance" -Direction Inbound -LocalPort 1433 -Protocol TCP -Action Allow # Add SQL Server Browser Local Firewall Rule New-NetFirewallRule -DisplayName "SQLServer Browser service" -Direction Inbound -LocalPort 1434 -Protocol UDP -Action Allow
I hope this was a useful SQL Tip. I have another post that relates to Windows Ports- How to Find Which Process is Listening on a Port in Windows
1 Comment
[…] ports to remember in the life of a DBA may include:# SQL Server (1433)# RedShift (5439)# PostgreSQL (5432)# MySQL (3306)# Oracle […]