How to Enable Windows Firewall with PowerShell
How to Enable Windows Firewall with PowerShell
This post is contains a demo on how to enable Windows Firewall with PowerShell in Windows Server.
This might be needed if you have discovered Windows Firewall is disabled on your or multiple computers, or you might want to re-enable it after disabling this for a test (see my other post on disabling instead of enabling).
Enabling Windows Firewall with PowerShell can be done by going through the following steps:
# Understand Windows Firewall Profiles
# Get-NetFirewallProfile PowerShell
# Set-NetFirewallProfile PowerShell
Understand Windows Firewall Profiles
Before running any command or script on your machine, it’s important for us to understand everything that it’s doing. In the command below we are disabling all 3 profiles:
# Domain – For when you are connected to a Domain Controller (computer connected to AD).
# Private – For your home or private networks.
# Public – For public WIFI locations such as coffee shops etc.
For more information on this, see this link – Microsoft Docs: Windows Firewall Profiles
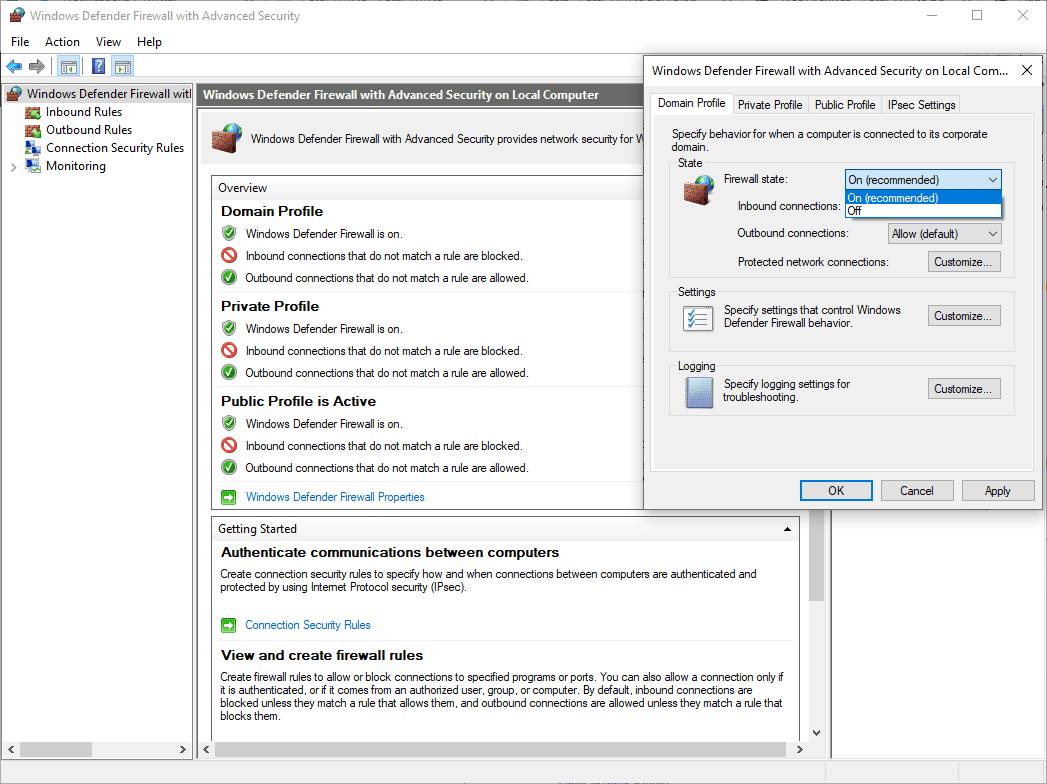
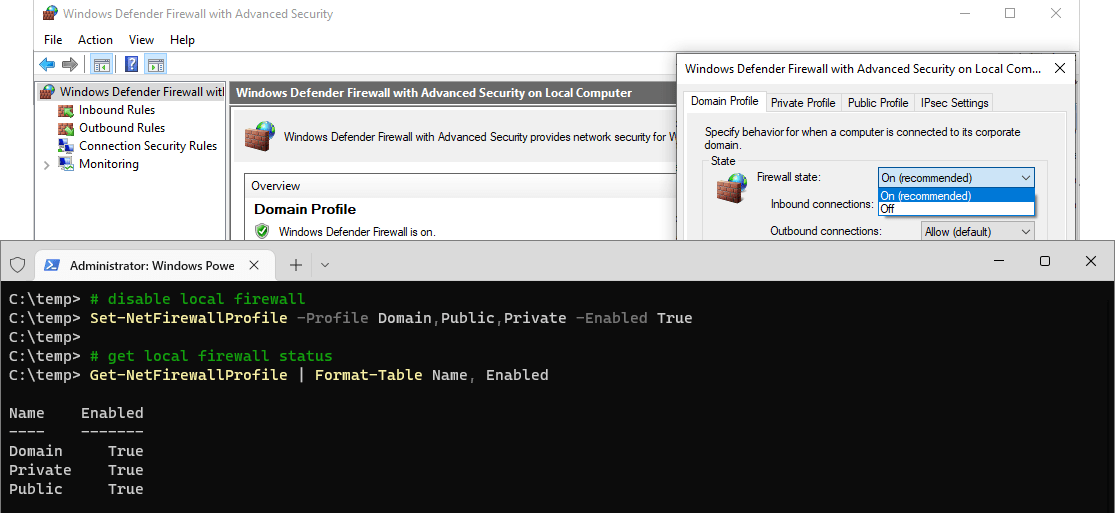
Also remember, all of this can be viewed and changed via GUI to help with understandings >
Get-NetFirewallProfile PowerShell
PowerShell commands follow standards and use verb-noun pairs for cmdlets. The verb at the start of the command describes the action the cmdlet performs, and the noun part is the action being performed. Here’s a list of Common Verbs, another Microsoft Docs link. The place of truth as I call it.
In this demo, we’re running Get-NetFirewallProfile with Format-Table
We’re getting the Firewall Profile status, and also formatting it into a table after a pipe ‘|’ –
# get local firewall status Get-NetFirewallProfile | Format-Table Name, Enabled
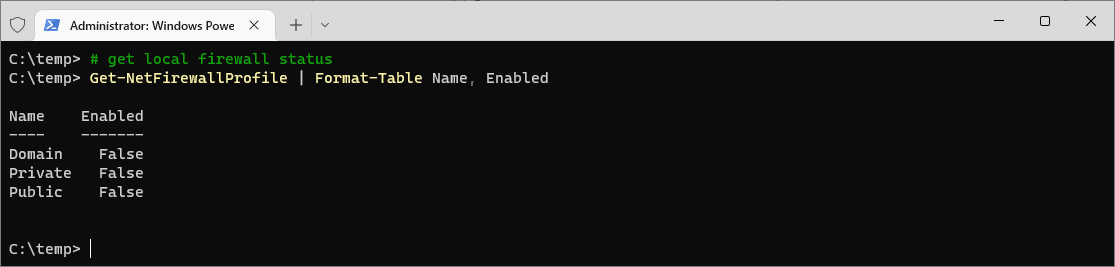
In the example above, the Windows Firewall is disabled, showing as ‘False‘.
Set-NetFirewallProfile PowerShell
We’re switching the cmdlet we ran above from Get to Set here (following on from verb-noun cmdlet descriptions).
To be able to run this; we have to open PowerShell or Windows Terminal as Administrator.
Set-NetFirewallProfile is being executed below, which enables all Profiles of the Local Windows Firewall –
# disable local firewall Set-NetFirewallProfile -Profile Domain,Public,Private -Enabled True # get local firewall status Get-NetFirewallProfile | Format-Table Name, Enabled
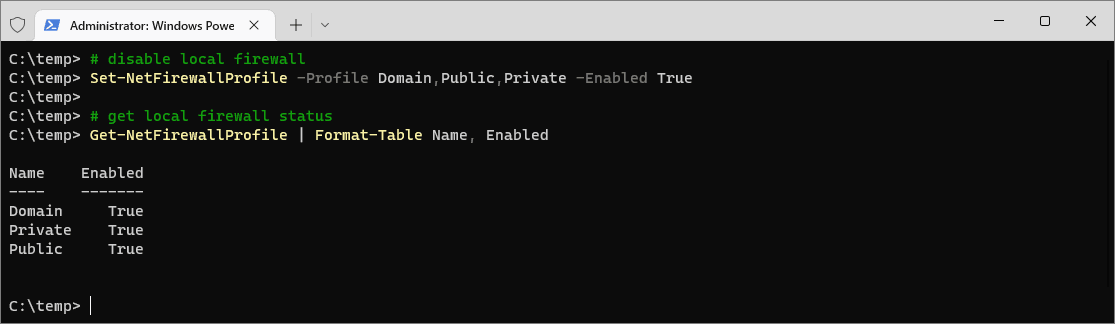
I followed the change by another run of Get-NetFirewallProfile to verify the change.

2 Comments
[…] Internal follow-up links: # How To Disable Windows Firewall With PowerShell# How To Enable Windows Firewall With PowerShell […]
[…] posts I have on this include the following:# How to Check Windows Firewall Status with PowerShell# How to Enable Windows Firewall with PowerShell# How to Disable Windows Firewall with […]